Hello NetBird Community!
March was packed. We shipped Layer 4 proxy support in v0.67, published two full video tutorials on Jellyfin and Authentik, met a ton of you at KubeCon Amsterdam, and landed a new case study from Solwr. Let's get into it.
Layer 4 Reverse Proxy: TLS, TCP, and UDP Support (v0.67)
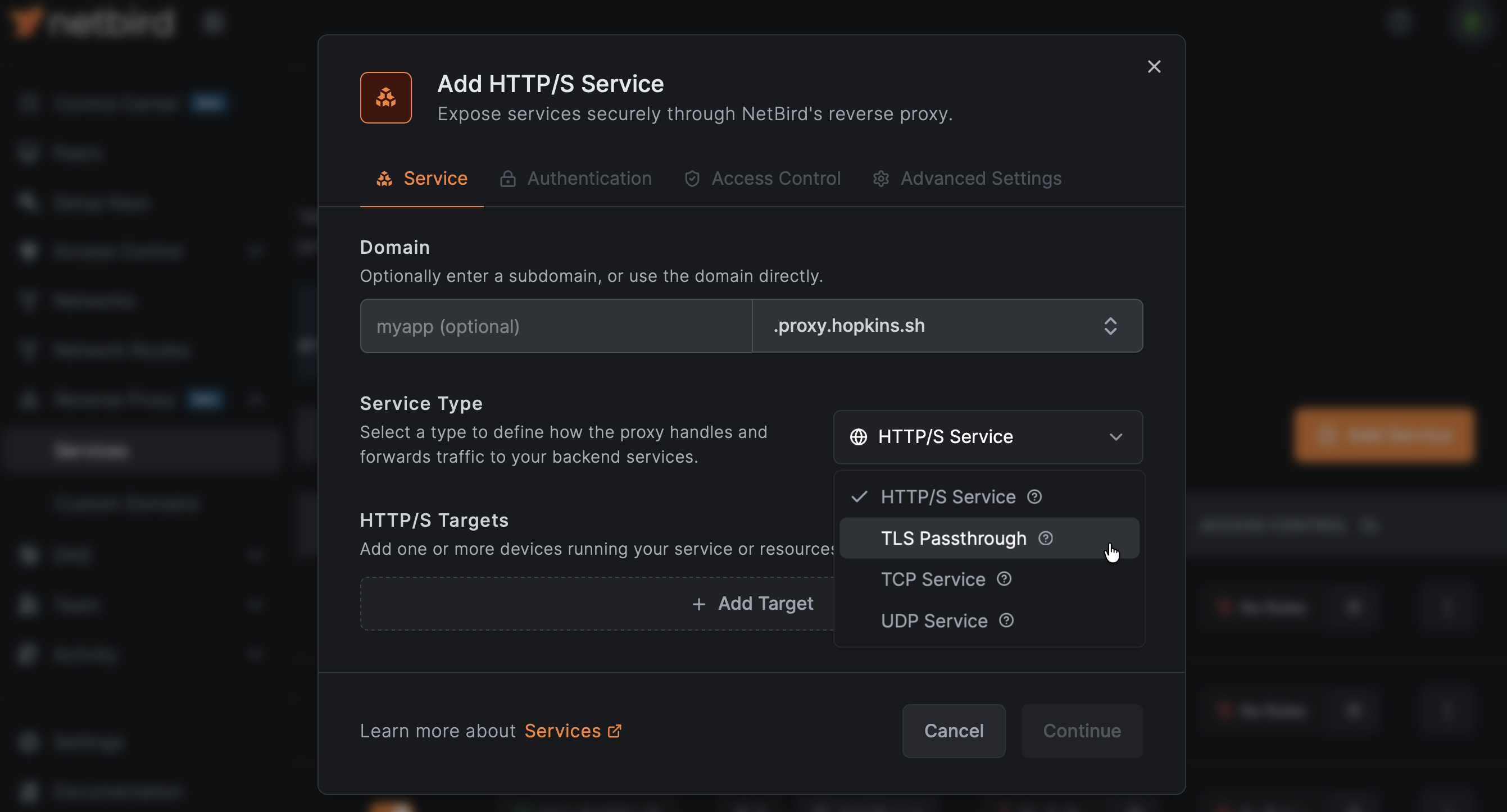
This was one of the most requested features since the reverse proxy launched. NetBird v0.67 extends the built-in reverse proxy beyond HTTP/HTTPS with Layer 4 capabilities, supporting TLS passthrough, raw TCP, and UDP traffic. This means you can now expose non-HTTP services like databases, game servers, VoIP endpoints, and legacy applications through the reverse proxy without wrapping them in HTTP.
On top of L4 support, this release also adds:
- Header-based authentication for proxy services
- Access restrictions for more granular control over who can reach exposed services
- Session idle timeout so inactive sessions don't hang around forever
- Health check flag and daemon status output in
- Reverse proxy cluster APIs and domain-based targeting
- Automatic engine restart when peer IP changes
Full release article here .
Jellyfin Media Server: Self-Host Your Movies, TV, and Music
Streaming services keep getting more expensive and content keeps rotating off platforms. Jellyfin lets you take your own media library and turn it into something that looks and feels like Netflix, running on your hardware with no subscription fees.
We published a full guide covering the entire setup: Docker Compose through Portainer on Ubuntu Server, storage planning for large media libraries, enabling Intel Quick Sync for hardware transcoding, and setting up secure remote access with NetBird so you can stream from anywhere. We also compare Jellyfin to Plex and Emby and why Jellyfin is the way to go if you want full control with zero strings attached.
Learn more: Knowledge Hub article
Self-Hosting NetBird with Authentik
For production self-hosted deployments, pairing NetBird with an external identity provider gives you SSO, multi-factor authentication, and centralized user management. This guide walks through the full setup: deploying NetBird on a VPS with the install script, running Authentik in the same Docker stack with a NetBird client sidecar, and exposing Authentik through the built-in reverse proxy with automatic TLS.
The cool part is the NetBird sidecar pattern. You add a NetBird client container to Authentik's Docker Compose stack with a static IP. That client acts as a routing peer, so NetBird can reach anything on that Docker network. The reverse proxy then uses that routing peer to expose Authentik under your domain. No separate Nginx, Caddy, or proxy stack required.
Learn more: Knowledge Hub article
Customer Spotlight: Solwr Replaces Two VPNs with NetBird
Solwr is one of Norway's leading logistics technology companies. Approximately one-third of all groceries in Norway pass through systems built by Solwr. They were running two separate VPN services, Fortinet and OpenVPN, and neither was cutting it. Fortinet's client kept breaking on updated operating systems, OpenVPN lacked domain-based split tunneling for Azure, and neither had proper access control based on identity groups.
Solwr replaced both with NetBird. The migration was fast, user adoption exceeded expectations, and they now manage their entire network configuration as code using NetBird's Terraform provider and API. When they found a bug, the fix was released within days.
Read the full story: Solwr case study
Implementing Zero Trust with NetBird
We published a practical guide to implementing Zero Trust Architecture aligned with NIST SP 800-207. This isn't a theoretical overview. It walks through planning, identity integration, access policies, routing peers, high availability, and monitoring with real NetBird configuration.
The key takeaways: plan before you configure, start small with one or two resources and iterate, make your IdP the single source of truth, run at least two routing peers for anything critical, and enable traffic events early so you can refine policies using real data instead of guessing.
Learn more: Knowledge Hub article | Full docs walkthrough
KubeCon Amsterdam Recap

The NetBird team was at KubeCon + CloudNativeCon Europe in Amsterdam (March 23-26) at booth 951. We had an amazing time meeting users, getting direct feedback, and talking shop with the cloud native community. Thank you to everyone who stopped by. The conversations about how you're using NetBird in production, from homelab setups to enterprise multi-cloud deployments, are what keeps us motivated. If we missed you this time, catch us at the next one.
Thank You!
Thank you for being part of the NetBird community. Your feedback, GitHub issues, and ideas continue to shape what we build. If you haven't already, come hang out with us on Slack or star us on GitHub .
– Team NetBird
Check out the changelog to stay on top of all the product releases. Follow NetBird on LinkedIn !
