We are happy to announce the release of NetBird Easy SSH. With NetBird Easy SSH, you can now SSH to your machines in your network without managing the keys.
SSH keys are one of the mechanisms for controlling access to IT resources. Like WireGuard keys, the user generates a private/public key pair. The private part of the key stays on the user's machine, and the public one can be freely shared and added to the authorized keys on the resource to be accessed.
Can SSH Keys Management be Painful?
As a software engineer, I use SSH daily to access remote servers and my Raspberry PIs running at home. While the SSH key distribution might not be a problem for a small home infrastructure, the hassle comes when there are many users and resources to access. Think of a fleet of IoT devices that require remote access and control; SSH keys management and rotation can be painful.
Throughout my career, I've seen different solutions that address the SSH key distribution problem ranging from custom scripts to Ansible playbooks and Terraform. They somehow work, but at NetBird, we decide to make it much simpler!
Shortly About NetBird
NetBird offers a simple way to connect IT resources regardless of location, whether a Linux server is running in the data center, a VM in the cloud or a Raspberry PI hosted at home. There is no need to configure a firewall or a router, have a public static IP address and setup VPN server. NetBird does all this automatically, adding SSO and an extra access control layer on top.
Every resource that runs the NetBird agent automatically joins your private WireGuard-based peer-to-peer network, even if it is behind NAT. At this point, you can connect to the remote resources, but you are still unable to SSH simply because the key is not there. Why not distribute it automatically as well?
open-source
NetBird is an open-source project. If you like what we do, give us a ⭐ on GitHub. Thank you!
A Simpler Way to Manage SSH Keys
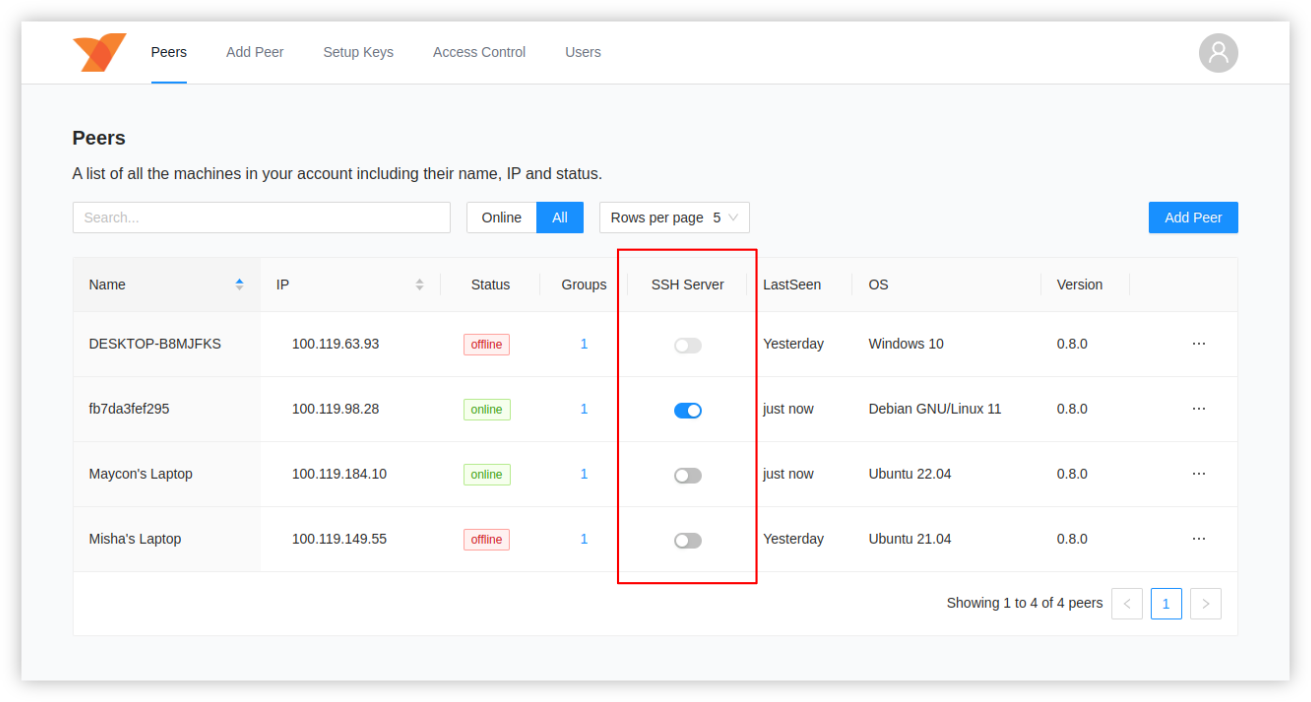
The NetBird v0.8.0 release adds an embedded SSH server to the agent that is easily enabled remotely through the Management Web UI. It accepts incoming SSH connections from the private NetBird network and only from the allowed resources.
tip
The SSH server feature is experimental and, by default is disabled on every agent. It can be enabled for each peer individually in the Peers tab by toggling the SSH Server switch.
But how does the agent get public keys from other peers? Starting v0.8.0, every SSH agent generates a private/public SSH key pair and advertises the public part to other network participants through the Management service storing the private part locally.
Every agent receives an update from the Management service that includes a list of public SSH keys of the peers allowed to access the machine. The SSH server updates the authorized keys list.
info
If the administrator revoked the machine's network access, the SSH access wouldn't be possible since the connection is not available anymore.
The NetBird SSH command
Besides the embedded SSH server, we added a new netbird ssh command to the agent. It is not possible to use the system's default SSH client.
For the time being, you need privilege access rights to run this command:
sudo netbird ssh <PEER IP>
Combined with the access control feature, this mechanism allows quick and hassles-free remote SSH access to your IT resources without managing SSH keys. A sweet bonus is that off-boarding becomes more straightforward as removing a user from the network automatically revokes SSH access.
Get started with NetBird
- Start using NetBird today: https://app.netbird.io
- Make sure to star us on GitHub
- Follow us on Twitter
- Join our Slack Channel
- NetBird release page on GitHub: v0.8.0
